Accessing your security log
The security log lists all actions performed within the last 90 days.
-
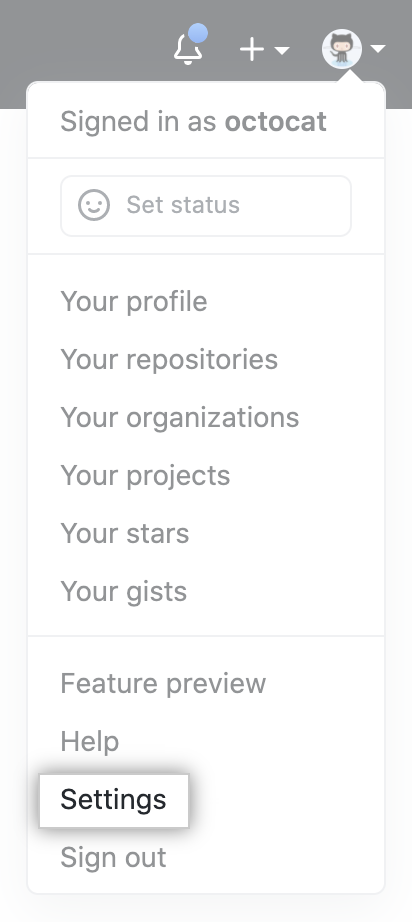
In the upper-right corner of any page, click your profile photo, then click Settings.
-
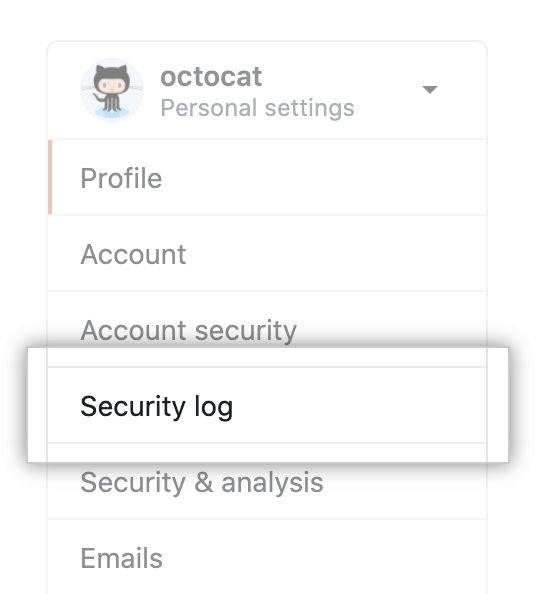
In the user settings sidebar, click Security log.
Searching your security log
The log lists the following information about each action:
- Which repository an action was performed in
- The user that performed the action
- The action that was performed
- Which country the action took place in
- The date and time the action occurred
Note that you cannot search for entries using text. You can, however, construct search queries using a variety of filters. Many operators used when querying the log, such as -, >, or <, match the same format as searching across GitHub Enterprise Server. For more information, see "Searching on GitHub."
Search based on operation
Use the operation qualifier to limit actions to specific types of operations. For example:
operation:accessfinds all events where a resource was accessed.operation:authenticationfinds all events where an authentication event was performed.operation:createfinds all events where a resource was created.operation:modifyfinds all events where an existing resource was modified.operation:removefinds all events where an existing resource was removed.operation:restorefinds all events where an existing resource was restored.operation:transferfinds all events where an existing resource was transferred.
Search based on repository
Use the repo qualifier to limit actions to a specific repository. For example:
repo:my-org/our-repofinds all events that occurred for theour-reporepository in themy-orgorganization.repo:my-org/our-repo repo:my-org/another-repofinds all events that occurred for both theour-repoandanother-reporepositories in themy-orgorganization.-repo:my-org/not-this-repoexcludes all events that occurred for thenot-this-reporepository in themy-orgorganization.
Note that you must include the account name within the repo qualifier; searching for just repo:our-repo will not work.
Search based on the user
The actor qualifier can scope events based on who performed the action. For example:
actor:octocatfinds all events performed byoctocat.actor:octocat actor:hubotfinds all events performed by bothoctocatandhubot.-actor:hubotexcludes all events performed byhubot.
Note that you can only use a GitHub Enterprise Server username, not an individual's real name.
Search based on the action performed
The events listed in your security log are triggered by your actions. Actions are grouped into the following categories:
| Category name | Description |
|---|---|
oauth_access | Contains all activities related to OAuth Apps you've connected with. |
profile_picture | Contains all activities related to your profile picture. |
project | Contains all activities related to project boards. |
public_key | Contains all activities related to your public SSH keys. |
repo | Contains all activities related to the repositories you own. |
team | Contains all activities related to teams you are a part of. |
two_factor_authentication | Contains all activities related to two-factor authentication. |
user | Contains all activities related to your account. |
Security log actions
An overview of some of the most common actions that are recorded as events in the security log.
oauth_access category actions
| Action | Description |
|---|---|
create | Triggered when you grant access to an OAuth App. |
destroy | Triggered when you revoke an OAuth App's access to your account. |
profile_picture category actions
| Action | Description |
|---|---|
update | Triggered when you set or update your profile picture. |
project category actions
| Action | Description |
|---|---|
access | Triggered when a project board's visibility is changed. |
create | Triggered when a project board is created. |
rename | Triggered when a project board is renamed. |
update | Triggered when a project board is updated. |
delete | Triggered when a project board is deleted. |
link | Triggered when a repository is linked to a project board. |
unlink | Triggered when a repository is unlinked from a project board. |
update_user_permission | Triggered when an outside collaborator is added to or removed from a project board or has their permission level changed. |
public_key category actions
| Action | Description |
|---|---|
create | Triggered when you add a new public SSH key to your GitHub Enterprise Server account. |
delete | Triggered when you remove a public SSH key to your GitHub Enterprise Server account. |
repo category actions
| Action | Description |
|---|---|
access | Triggered when you a repository you own is switched from "private" to "public" (or vice versa). |
add_member | Triggered when a GitHub Enterprise Server user is given collaboration access to a repository. |
add_topic | Triggered when a repository owner adds a topic to a repository. |
archived | Triggered when a repository owner archives a repository. |
config.disable_anonymous_git_access | Triggered when anonymous Git read access is disabled in a public repository. |
config.enable_anonymous_git_access | Triggered when anonymous Git read access is enabled in a public repository. |
config.lock_anonymous_git_access | Triggered when a repository's anonymous Git read access setting is locked. |
config.unlock_anonymous_git_access | Triggered when a repository's anonymous Git read access setting is unlocked. |
create | Triggered when a new repository is created. |
destroy | Triggered when a repository is deleted. |
remove_member | Triggered when a GitHub Enterprise Server user is removed from a repository as a collaborator. |
remove_topic | Triggered when a repository owner removes a topic from a repository. |
rename | Triggered when a repository is renamed. |
transfer | Triggered when a repository is transferred. |
transfer_start | Triggered when a repository transfer is about to occur. |
unarchived | Triggered when a repository owner unarchives a repository. |
team category actions
| Action | Description |
|---|---|
add_member | Triggered when a member of an organization you belong to adds you to a team. |
add_repository | Triggered when a team you are a member of is given control of a repository. |
create | Triggered when a new team in an organization you belong to is created. |
destroy | Triggered when a team you are a member of is deleted from the organization. |
remove_member | Triggered when a member of an organization is removed from a team you are a member of. |
remove_repository | Triggered when a repository is no longer under a team's control. |
two_factor_authentication category actions
| Action | Description |
|---|---|
enabled | Triggered when two-factor authentication is enabled. |
disabled | Triggered when two-factor authentication is disabled. |
user category actions
| Action | Description |
|---|---|
add_email | Triggered when you add a new email address. |
create | Triggered when you create a new user account. |
change_password | Triggered when you change your password. |
forgot_password | Triggered when you ask for a password reset. |
hide_private_contributions_count | Triggered when you hide private contributions on your profile. |
login | Triggered when you log in to your GitHub Enterprise Server instance. |
failed_login | Triggered when you failed to log in successfully. |
remove_email | Triggered when you remove an email address. |
rename | Triggered when you rename your account. |
show_private_contributions_count | Triggered when you publicize private contributions on your profile. |
two_factor_requested | Triggered when GitHub Enterprise Server asks you for your two-factor authentication code. |
user_status category actions
| Action | Description |
|---|---|
update | Triggered when you set or change the status on your profile. For more information, see "Setting a status." |
destroy | Triggered when you clear the status on your profile. |