Accessing the audit log
The audit log lists events triggered by activities that affect your organization within the last 90 days. Only owners can access an organization's audit log.
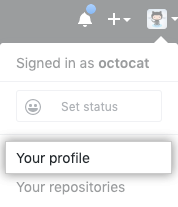
- In the top right corner of GitHub Enterprise Server, click your profile photo, then click Your profile.
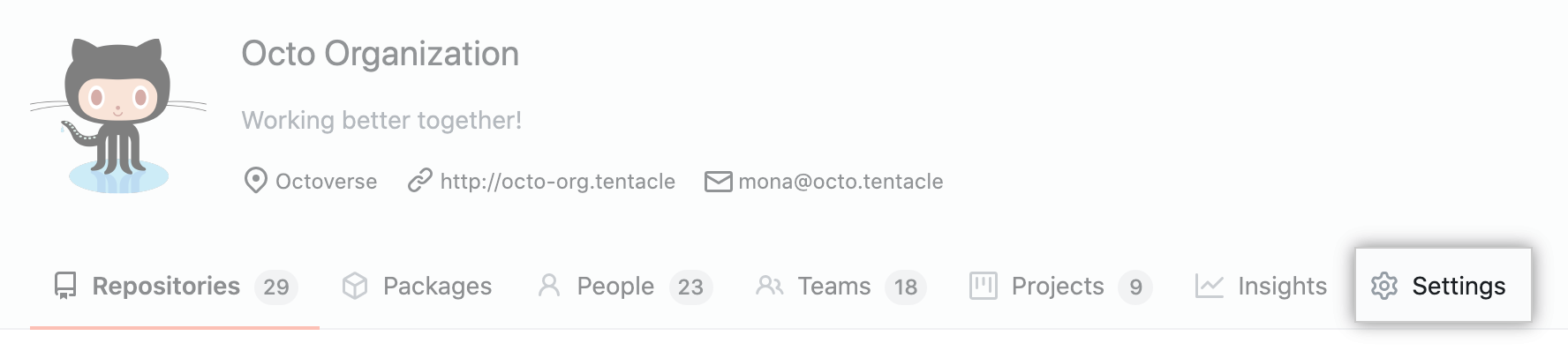
- On the left side of your profile page, under "Organizations", click the icon for your organization.

- Under your organization name, click Settings.
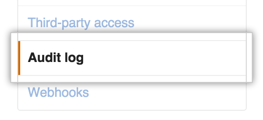
- In the Settings sidebar, click Audit log.
Searching the audit log
The log lists the following information about each action:
- Which repository an action was performed in
- The user that performed the action
- The action that was performed
- Which country the action took place in
- The date and time the action occurred
Note that you cannot search for entries using text. You can, however, construct search queries using a variety of filters. Many operators used when querying the log, such as -, >, or <, match the same format as searching across GitHub Enterprise Server. For more information, see "Searching on GitHub."
Search based on operation
Use the operation qualifier to limit actions to specific types of operations. For example:
operation:accessfinds all events where a resource was accessed.operation:authenticationfinds all events where an authentication event was performed.operation:createfinds all events where a resource was created.operation:modifyfinds all events where an existing resource was modified.operation:removefinds all events where an existing resource was removed.operation:restorefinds all events where an existing resource was restored.operation:transferfinds all events where an existing resource was transferred.
Search based on repository
Use the repo qualifier to limit actions to a specific repository. For example:
repo:my-org/our-repofinds all events that occurred for theour-reporepository in themy-orgorganization.repo:my-org/our-repo repo:my-org/another-repofinds all events that occurred for both theour-repoandanother-reporepositories in themy-orgorganization.-repo:my-org/not-this-repoexcludes all events that occurred for thenot-this-reporepository in themy-orgorganization.
Note that you must include the account name within the repo qualifier; searching for just repo:our-repo will not work.
Search based on the user
The actor qualifier can scope events based on who performed the action. For example:
actor:octocatfinds all events performed byoctocat.actor:octocat actor:hubotfinds all events performed by bothoctocatandhubot.-actor:hubotexcludes all events performed byhubot.
Note that you can only use a GitHub Enterprise Server username, not an individual's real name.
Search based on the action performed
To search for specific events, use the action qualifier in your query. Actions listed in the audit log are grouped within the following categories:
| Category name | Description |
|---|---|
discussion_post | Contains all activities related to discussions posted to a team page. |
discussion_post_reply | Contains all activities related to replies to discussions posted to a team page. |
hook | Contains all activities related to webhooks. |
integration_installation_request | Contains all activities related to organization member requests for owners to approve integrations for use in the organization. |
issue | Contains activities related to deleting an issue. |
org | Contains activities related to organization membership. |
organization_label | Contains all activities related to default labels for repositories in your organization. |
oauth_application | Contains all activities related to OAuth Apps. |
profile_picture | Contains all activities related to your organization's profile picture. |
project | Contains all activities related to project boards. |
protected_branch | Contains all activities related to protected branches. |
repo | Contains activities related to the repositories owned by your organization. |
repository_dependency_graph | Contains repository-level activities related to enabling or disabling the dependency graph for a repository. For more information, see "About the dependency graph." |
repository_vulnerability_alert | Contains all activities related to Dependabot alerts for vulnerable dependencies. |
team | Contains all activities related to teams in your organization. |
team_discussions | Contains activities related to managing team discussions for an organization. |
You can search for specific sets of actions using these terms. For example:
action:teamfinds all events grouped within the team category.-action:hookexcludes all events in the webhook category.
Each category has a set of associated actions that you can filter on. For example:
action:team.createfinds all events where a team was created.-action:hook.events_changedexcludes all events where the events on a webhook have been altered.
Search based on time of action
Use the created qualifier to filter events in the audit log based on when they occurred. Date formatting must follow the ISO8601 standard, which is YYYY-MM-DD (year-month-day). You can also add optional time information THH:MM:SS+00:00 after the date, to search by the hour, minute, and second. That's T, followed by HH:MM:SS (hour-minutes-seconds), and a UTC offset (+00:00).
When you search for a date, you can use greater than, less than, and range qualifiers to further filter results. For more information, see "Understanding the search syntax."
For example:
created:2014-07-08finds all events that occurred on July 8th, 2014.created:>=2014-07-08finds all events that occurred on or after July 8th, 2014.created:<=2014-07-08finds all events that occurred on or before July 8th, 2014.created:2014-07-01..2014-07-31finds all events that occurred in the month of July 2014.
The audit log contains data for the past 90 days, but you can use the created qualifier to search for events earlier than that.
Search based on location
Using the qualifier country, you can filter events in the audit log based on the originating country. You can use a country's two-letter short code or its full name. Keep in mind that countries with spaces in their name will need to be wrapped in quotation marks. For example:
country:definds all events that occurred in Germany.country:Mexicofinds all events that occurred in Mexico.country:"United States"all finds events that occurred in the United States.
Using the audit log API
You can interact with the audit log using the GraphQL API.
Note: The audit log GraphQL API is available for organizations using GitHub Enterprise.
To ensure a secure IP and maintain compliance for your organization, you can use the audit log GraphQL API to keep copies of your audit log data and monitor:
- Access to your organization or repository settings
- Changes in permissions
- Added or removed users in an organization, repository, or team
- Users being promoted to admin
- Changes to permissions of a GitHub App
The GraphQL response can include data for up to 90 to 120 days.
For example, you can make a GraphQL request to see all the new organization members added to your organization. For more information, see the "GraphQL API Audit Log."
Audit log actions
An overview of some of the most common actions that are recorded as events in the audit log.
discussion_post category actions
| Action | Description |
|---|---|
update | Triggered when a team discussion post is edited. |
destroy | Triggered when a team discussion post is deleted. |
discussion_post_reply category actions
| Action | Description |
|---|---|
update | Triggered when a reply to a team discussion post is edited. |
destroy | Triggered when a reply to a team discussion post is deleted. |
hook category actions
| Action | Description |
|---|---|
create | Triggered when a new hook was added to a repository owned by your organization. |
config_changed | Triggered when an existing hook has its configuration altered. |
destroy | Triggered when an existing hook was removed from a repository. |
events_changed | Triggered when the events on a hook have been altered. |
integration_installation_request category actions
| Action | Description |
|---|---|
create | Triggered when an organization member requests that an organization owner install an integration for use in the organization. |
close | Triggered when a request to install an integration for use in an organization is either approved or denied by an organization owner, or canceled by the organization member who opened the request. |
issue category actions
| Action | Description |
|---|---|
destroy | Triggered when an organization owner or someone with admin permissions in a repository deletes an issue from an organization-owned repository. |
org category actions
| Action | Description |
|---|---|
disable_member_team_creation_permission | Triggered when an organization owner limits team creation to owners. For more information, see "Setting team creation permissions in your organization." |
disable_two_factor_requirement | Triggered when an owner disables a two-factor authentication requirement for all members and outside collaborators in an organization. |
enable_member_team_creation_permission | Triggered when an organization owner allows members to create teams. For more information, see "Setting team creation permissions in your organization." |
enable_two_factor_requirement | Triggered when an owner requires two-factor authentication for all members and outside collaborators in an organization. |
invite_member | Triggered when a new user was invited to join your organization. |
remove_member | Triggered when an owner removes a member from an organization or when two-factor authentication is required in an organization and an organization member doesn't use 2FA or disables 2FA. Also triggered when an organization member removes themselves from an organization. |
remove_outside_collaborator | Triggered when an owner removes an outside collaborator from an organization or when two-factor authentication is required in an organization and an outside collaborator does not use 2FA or disables 2FA. |
update_default_repository_permission | Triggered when an owner changes the default repository permission level for organization members. |
update_member | Triggered when an owner changes a person's role from owner to member or member to owner. |
update_member_repository_creation_permission | Triggered when an owner changes the create repository permission for organization members. |
organization_label category actions
| Action | Description |
|---|---|
create | Triggered when a default label is created. |
update | Triggered when a default label is edited. |
destroy | Triggered when a default label is deleted. |
oauth_application category actions
| Action | Description |
|---|---|
create | Triggered when a new OAuth App is created. |
destroy | Triggered when an existing OAuth App is deleted. |
reset_secret | Triggered when an OAuth App's client secret is reset. |
revoke_tokens | Triggered when an OAuth App's user tokens are revoked. |
transfer | Triggered when an existing OAuth App is transferred to a new organization. |
profile_picture category actions
| Action | Description |
|---|---|
| update | Triggered when you set or update your organization's profile picture. |
project category actions
| Action | Description |
|---|---|
create | Triggered when a project board is created. |
link | Triggered when a repository is linked to a project board. |
rename | Triggered when a project board is renamed. |
update | Triggered when a project board is updated. |
delete | Triggered when a project board is deleted. |
unlink | Triggered when a repository is unlinked from a project board. |
update_org_permission | Triggered when the base-level permission for all organization members is changed or removed. |
update_team_permission | Triggered when a team's project board permission level is changed or when a team is added or removed from a project board. |
update_user_permission | Triggered when an organization member or outside collaborator is added to or removed from a project board or has their permission level changed. |
protected_branch category actions
| Action | Description |
|---|---|
create | Triggered when branch protection is enabled on a branch. |
destroy | Triggered when branch protection is disabled on a branch. |
update_admin_enforced | Triggered when branch protection is enforced for repository administrators. |
update_require_code_owner_review | Triggered when enforcement of required Code Owner review is updated on a branch. |
dismiss_stale_reviews | Triggered when enforcement of dismissing stale pull requests is updated on a branch. |
update_signature_requirement_enforcement_level | Triggered when enforcement of required commit signing is updated on a branch. |
update_pull_request_reviews_enforcement_level | Triggered when enforcement of required pull request reviews is updated on a branch. |
update_required_status_checks_enforcement_level | Triggered when enforcement of required status checks is updated on a branch. |
update_strict_required_status_checks_policy | Triggered when the requirement for a branch to be up to date before merging is changed. |
rejected_ref_update | Triggered when a branch update attempt is rejected. |
policy_override | Triggered when a branch protection requirement is overridden by a repository administrator. |
update_allow_force_pushes_enforcement_level | Triggered when force pushes are enabled or disabled for a protected branch. |
update_allow_deletions_enforcement_level | Triggered when branch deletion is enabled or disabled for a protected branch. |
update_linear_history_requirement_enforcement_level | Triggered when required linear commit history is enabled or disabled for a protected branch. |
repo category actions
| Action | Description |
|---|---|
access | Triggered when a user changes the visibility of a repository in the organization. |
actions_enabled | Triggered when GitHub Actions is enabled for a repository. Can be viewed using the UI. This event is not included when you access the audit log using the REST API. For more information, see "Using the REST API." |
add_member | Triggered when a user accepts an invitation to have collaboration access to a repository. |
add_topic | Triggered when a repository admin adds a topic to a repository. |
archived | Triggered when a repository admin archives a repository. |
config.disable_anonymous_git_access | Triggered when anonymous Git read access is disabled in a public repository. |
config.enable_anonymous_git_access | Triggered when anonymous Git read access is enabled in a public repository. |
config.lock_anonymous_git_access | Triggered when a repository's anonymous Git read access setting is locked. |
config.unlock_anonymous_git_access | Triggered when a repository's anonymous Git read access setting is unlocked. |
create | Triggered when a new repository is created. |
destroy | Triggered when a repository is deleted. |
enable | Triggered when a repository is reenabled. |
remove_member | Triggered when a user is removed from a repository as a collaborator. |
remove_topic | Triggered when a repository admin removes a topic from a repository. |
rename | Triggered when a repository is renamed. |
transfer | Triggered when a repository is transferred. |
transfer_start | Triggered when a repository transfer is about to occur. |
unarchived | Triggered when a repository admin unarchives a repository. |
repository_dependency_graph category actions
| Action | Description |
|---|---|
disable | Triggered when a repository owner or person with admin access to the repository disables the dependency graph for a repository. For more information, see "About the dependency graph." |
enable | Triggered when a repository owner or person with admin access to the repository enables the dependency graph for a repository. |
repository_vulnerability_alert category actions
| Action | Description |
|---|---|
create | Triggered when GitHub Enterprise Server creates a security alert for a repository that uses a vulnerable dependency. For more information, see "About alerts for vulnerable dependencies." |
dismiss | Triggered when an organization owner or person with admin access to the repository dismisses a security alert about a vulnerable dependency. |
resolve | Triggered when someone with write access to a repository pushes changes to update and resolve a vulnerability in a project dependency. |
team category actions
| Action | Description |
|---|---|
add_member | Triggered when a member of an organization is added to a team. |
add_repository | Triggered when a team is given control of a repository. |
change_parent_team | Triggered when a child team is created or a child team's parent is changed. |
change_privacy | Triggered when a team's privacy level is changed. |
create | Triggered when a new team is created. |
destroy | Triggered when a team is deleted from the organization. |
remove_member | Triggered when a member of an organization is removed from a team. |
remove_repository | Triggered when a repository is no longer under a team's control. |
team_discussions category actions
| Action | Description |
|---|---|
disable | Triggered when an organization owner disables team discussions for an organization. For more information, see "Disabling team discussions for your organization." |
enable | Triggered when an organization owner enables team discussions for an organization. |